Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
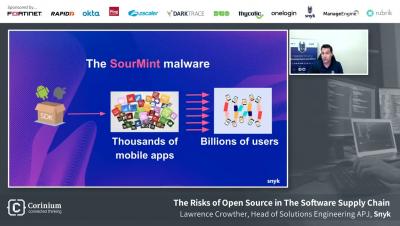
The Risks of Open Source in the Software Supply Chain with Lawrence Crowther, Snyk
Ask SME Anything: Why should IT leaders care about SSPM?
Delivering Electrons, Generating Data Lakes, and the Security of an Industrial Organization | Ep 25
CIS Control 6: Access Control Management
CIS Control 6 merges some aspects of CIS Control 4 (admin privileges) and CIS Control 14 (access based on need to know) into a single access control management group. Access control management is a critical component in maintaining information and system security, restricting access to assets based on role and need. It is important to grant, refuse, and remove access in a standardized, timely, and repeatable way across an entire organization.
CISSP Exam Pattern Changes, May 2021
On May 1, 2021, ISC² implemented a refreshed set of objectives for the CISSP certification exam for security professionals in order to keep it relevant to the latest technologies and cybersecurity standards, requirements and processes. New information security concepts, terms and acronyms have been added and others are better covered.
Encryption and authentication don't need to be painful! Here's how.
I had the pleasure of being at an in-person event recently. Aside from the joy it brought me to simply see people for the three-dimensional beings they are, it was of course incredible to connect with the Information Security community once more. Interestingly, a topic came up in quite a few of my conversations with fellow delegates. And it was one that I wasn’t expecting: encryption. It was often amiable, but on a couple of occasions eyes would roll.
Slack Security: FERPA and HIPAA Compliance
During the pandemic, healthcare and education providers scrambled to adapt to providing services remotely, using tools like Slack, Google Drive, and Zoom to continue connecting with patients and students. McKinsey tracked a spike in the use of telehealth solutions in April 2020 that was 78 times higher than in February 2020. And, by some estimates, more than 1.2 billion children worldwide were impacted by school closures due to the pandemic — some of whom were able to learn remotely.
Process Hunting with a Process
Quite often you are in the middle of a security incident or just combing through your data looking for signs of malicious activity, and you will want to trace the activity or relationships of a particular process. This can be a very time-consuming and frustrating task if you try to brute force things (copying/pasting parent and child process IDs over and over again). And in the heat of battle, you may miss one item that could have led you to something interesting.
What The Worst Attacks Of 2021 Can Teach Us On The Future Of Ransomware
Despite the steady drumbeat of hacks that are reported on a nearly weekly basis, it is safe to say that cybersecurity is still far from a “top of mind issue” for most people. Massive data breaches like Equifax, Marriott, and many, many more are chalked up to being yet another part of the modern life. While each of those cybersecurity incidents was quite serious in its own right, for the public whose data were compromised, they represented more of an inconvenience than a serious concern.