Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
The latest News and Information on Security Orchestration, Automation and Response.
Denmark's Largest Utility Company Accelerates Incident Response
As Denmark’s largest power, utility and telecommunications company servicing 1.5 million customers, Norlys understands the need for fast response to security alerts. When the company first started, the Norlys security team built their own log analytics and incident response capabilities from the ground up. This homegrown approach presented challenges, including manual workflows, too many repetitive tasks and difficult-to-maintain processes.
Splunk Data Stream Processor & Splunk Phantom - The Need For Speed
What is the benefit of combining the power of Data Stream Processor (DSP) and Splunk Phantom? I will give you a hint - the answer involves speed and extensibility. In today's security landscape, speed to detect and mitigate security attacks or outages is of the utmost importance. A slow response to a security incident can have a detrimental impact to your organization's bottom line.
Phishing Emails - Less Ocean, More Aquarium
Here at Splunk, when we discuss Splunk Phantom with customers we end up talking about phishing pretty frequently because it’s something like Olivia outlined in a recent blog post, "Between Two Alerts: Phishing Emails — Don’t Get Reeled In!", customers both encounter and talk to us about all the time. It makes a lot of sense — phishing is a super common issue that almost everyone deals with ad nauseum and it’s annoying to investigate.
Working in the SOC with Power Tools: Splunk and Polarity
Have you ever had to saw through a board by hand? I had to finish a partial cut by hand the other day while building a new mantle for my fireplace. It’s slow and difficult, and it often results in a lesser quality cut than one done with a power tool. It’s good exercise, though! We should all have to do it at least once so we appreciate our power tools more.
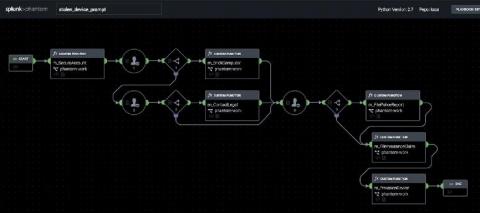
Adaptable Incident Response With Splunk Phantom Modular Workbooks
Splunk Phantom is a security orchestration, automation and response (SOAR) technology that lets customers automate repetitive security tasks, accelerate alert triage, and improve SOC efficiency. Case management features are also built into Phantom, including “workbooks,” that allow you to codify your security standard operating procedures into reusable templates.
Bringing Threat Intelligence to Security Playbooks - Recorded Future and Splunk Phantom
Connecting the dots for security analysts
Splunk Phantom Demo Video
Supercharged SOAR: Meet Splunk Phantom 4.9
The number of cyberattacks launched on organizations continues to rise every year. More attacks means more security alerts that security analysts have to triage each day. Many security teams have turned to a security orchestration, automation and response (SOAR) tool to help them automate the ever-increasing volume of security alerts, and respond to threats faster and more comprehensively.