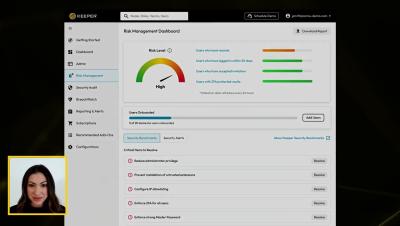
Keeper 101 | Enterprise: Risk Management Dashboard
The Keeper Risk Management Dashboard is a powerful feature of the Keeper Admin Console that provides comprehensive security posture information covering end-user deployment, utilization, cloud configuration, and event monitoring. This critical data helps administrators ensure that risks are remediated and compliance is enforced effectively. The Risk Management Dashboard monitors key metrics and leverages Keeper Security's Benchmarks to enforce the highest level of security in your environment across all users and devices.