Compliance vs ethics | TrustTalks - Ep 33 | Security and GRC Podcast
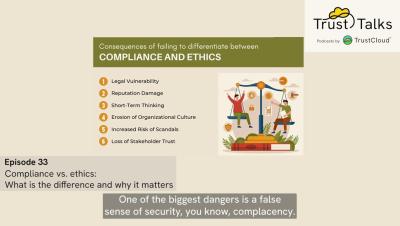
This podcast focuses on the crucial difference between compliance (adhering to laws and regulations) and ethics (upholding moral principles) in business. It highlights the risks of prioritising one over the other, advocating for a balanced approach to foster a strong ethical culture. Several case studies illustrate the consequences of neglecting either compliance or ethics. It also offers strategies for integrating both into business practices to enhance reputation, reduce risk, and improve decision-making.