Why All AI Can Be Exploited #security #ai #tech
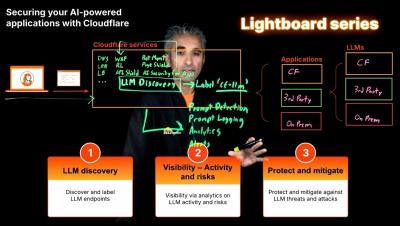
AI systems treat almost everything as a possible input channel, from PDFs and PowerPoints to text, music and more. Without a real separation between control plane instructions and data plane content, the attack surface keeps growing faster than most security programmes can contain.