The Most Dangerous Blind Spot in SaaS Architecture #saas #saassecurity #cloudsecurity #apisecurity
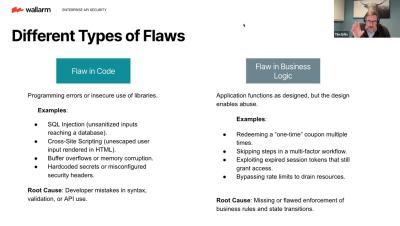
When data flows between two critical SaaS tools (like Salesforce and a CRM chatbot), you have zero visibility into that traffic. This leaves a gaping hole for attackers to exploit Business Logic Abuse. Since you can't see the traffic, you cannot monitor the attack. The Solution? Rigorous Vendor Management. Control Your Own Keys! The responsibility to protect your sensitive data is always yours, even in the cloud.