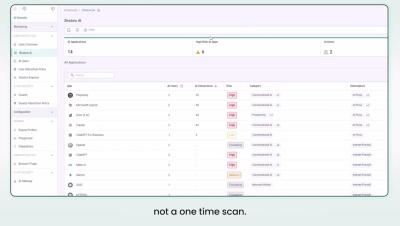
See, Govern, and Secure All AI Usage in Your Enterprise
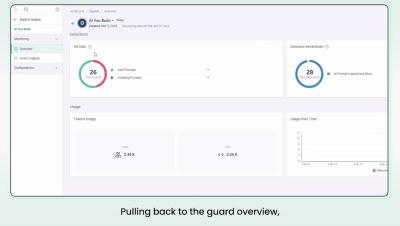
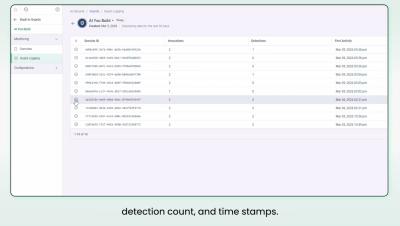
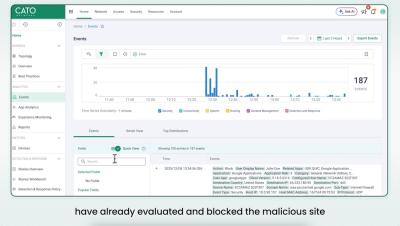
Do you happen to know which AI tools your employees are using right now, or what data they're sending into them? Cato AI Security automatically discovers every AI application in your environment, provides security teams with session-level visibility into how those tools are being used, and enforces data policies in real time, so employees can keep working and sensitive data stays where it belongs.