Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
What's New in Sysdig - October 2023
“What’s New in Sysdig” is back with the October 2023 edition! My name is Zain Ghani, based in Austin, Texas, joined by my colleague, Matt Baran, based in Los Angeles, California, to share our latest updates with you. The last few weeks have been really exciting at Sysdig.
Skeleton Keys and Local Admin Passwords: A Cautionary Tale
Picture yourself immersed in your favorite mystery novel, eagerly flipping through the pages as the suspense thickens. You’re enthralled, engrossed in the story of a hotel burglar with an uncanny ability to sneak into guest rooms without leaving telltale signs of break-ins or lock-picking. As you read on, you’re captivated – and stumped – by how this elusive bad actor can deftly close the doors behind them, leaving no clues.
PCI DSS Compliance Hardening Policy
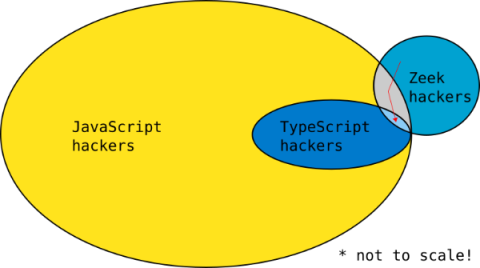
Writing a Zeek package in TypeScript with ZeekJS
Zeek® is the world’s most widely used network security monitoring platform and is the foundation for Corelight network evidence. In this blog I share how to write a Zeek package in TypeScript with a new capability called ZeekJS that was released as part of Zeek 6.0.
Revival Animal Health Network Announces Third-Party Data Breach
Headquartered in Orange City, Iowa, Revival Animal Health delivers business solutions for pet-oriented care and service providers; they offer pet healthcare products and animal supplies to pet professionals and individual pet owners. One way they provide services is via the e-commerce host CommerceV3. Revival Animal Health recently announced that CommerceV3 suffered a vulnerability, exposing 66,574 customer records.
A Deep Dive Into Cloud Security Assessments
Cloud platforms offer unparalleled scalability, flexibility, and cost-efficiency. However, the convenience and advantages of the cloud are accompanied by significant security challenges. Hackers are constantly trying to exploit weak cloud configuration settings, which is why it’s important to have visibility into the security of your organization’s cloud infrastructure.
Free Template: Vendor Post-Data Breach Questionnaire (2023)
UTMStack Unveils Commercial License for its Correlation Engine and SDK: A Boon for Organizations Developing SIEM or XDR Solutions
In a significant move to empower organizations in bolstering their security infrastructure, UTMstack has announced the commercialization of its Correlation Engine and Software Development Kit (SDK) under a commercial license. This strategic initiative paves the way for organizations aiming to develop their own Security Information and Event Management (SIEM) or Extended Detection and Response (XDR) solutions by leveraging the state-of-the-art features embedded in the UTMstack’s platform.
Detecting Network-Based Anomalies with Calico
In the vast digital landscape, the flow of data across networks is akin to water coursing through a city’s plumbing system. Just as impurities in water can signal potential issues, deviations in network traffic, termed as network inserted anomalies, can hint at cyber threats. These anomalies range from overt signs like unauthorized access attempts to subtler indicators like unusual data transfer patterns.