The future of cybersecurity: AI and SIEM working together
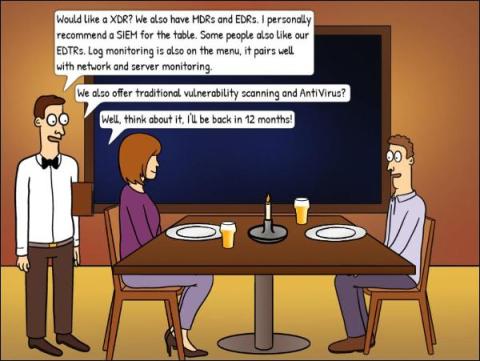
Imagine a world where your digital security isn't just a tall wall guarding against intruders but a sophisticated AI sentinel, always learning, always adapting. That's the world we're zooming into when we talk about the convergence of AI and Security Information and Event Management (SIEM) systems. This fusion is not just a fancy addition to the cybersecurity toolset; it's rapidly becoming a necessity for businesses that seek to stay ahead in this grand digital chess game against cyber threats. You should consider Exploring the Essentials of SIEM for Business Security further to help you understand better.