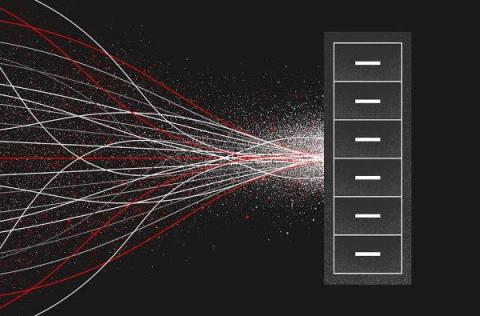
Log Management Key to Meeting OMB-21-31 Requirements
Last Summer, President Biden issued Executive Order 14028 to help boost and improve government cybersecurity operations in response to increased threats worldwide. Memorandum OMB-21-31 from the Office of Management and Budget soon followed, which explained the critical role data log collection and analysis play across all branches of the Federal Government.