Introducing Mend's Integration with Microsoft Defender for Cloud
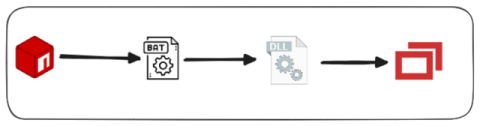
We’re excited to announce a powerful new integration between Mend.io and Microsoft Defender for Cloud (MDC)—a step forward in our mission to bring intelligent, actionable, and context-rich open source security directly into the cloud security workflow. As organizations embrace cloud-native architectures, security teams face the growing challenge of identifying and prioritizing the open source software risks that truly matter.