Accelerating Security Operations with Splunk and Foundation AI's First Open-Source Security Model
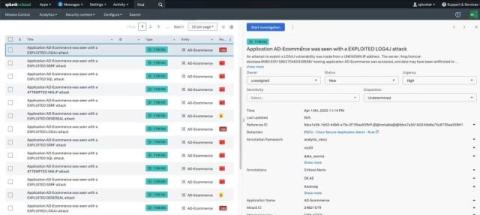
Cisco Foundation AI’s Foundation-sec-8b model brings a new wave of innovations and efficiency to security operations. As a purpose-built, open-weight Large Language Model (LLM) designed specifically for cybersecurity, Foundation-sec-8b enables security teams to act faster, reduce fatigue, and scale operations without compromising accuracy.