SAST vs. DAST for Security Testing: Unveiling the Differences
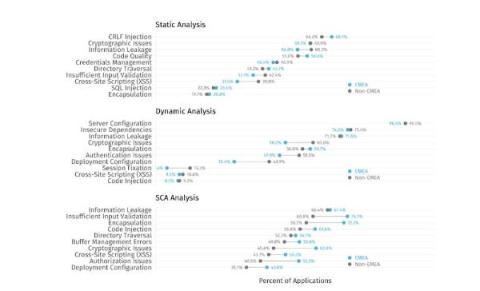
Application Security Testing (AST) encompasses various tools, processes, and approaches to scanning applications to uncover potential security issues. Static Application Security Testing (SAST) and Dynamic Application Security Testing (DAST) are popularly used security testing approaches that follow different methodologies of scanning application codes across different stages of a software development lifecycle.