Global SOC Survey Reveals Hope for SecOps Teams As Post-SOAR Hyperautomation Boosts Analyst Retention and Tenure
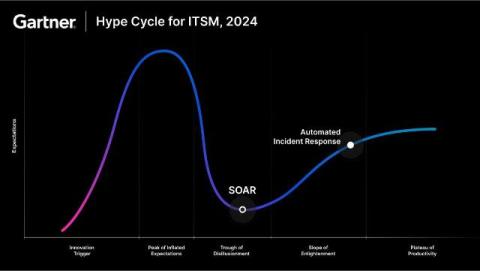
The SANS 2024 SOC Survey, a comprehensive new Torq-sponsored study, reveals that for the first time in decades, the tenure of SOC and Security Analysts is increasing. They’re choosing to remain at their posts for three-to-five years, up from an average of one-to-three years. Modern post-SOAR hyperautomation solutions are playing a significant role in alleviating the burdens these cybersecurity pros face.