Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
SSH Tunneling Explained
Although the typical use case of SSH is to access a remote server securely, you can also transfer files, forward local and remote ports, mount remote directories, redirect GUI, or even proxy arbitrary traffic (need I say SSH is awesome?). And this is just a small set of what’s possible with SSH.
The Power of Data: Calendar-based Policy Enforcement
A problem that is often discussed in the context of policy-as-code is how to get more people other than developers involved in policy authoring. Policy as code is still code, and while tooling and abstractions can help to some extent, the process still involves at least some level of development knowledge.
WhiteSource Cure: Automated Remediation for Developers
Keeping up with today’s rapidly evolving threat landscape is an ongoing battle for software development organizations, as many struggle to keep their assets and customers secure while keeping up with the competitive pace of software delivery.
Securing Internal Applications
SnykCon 2021 Gathers Thousands of Developers to Advance the Global DevSecOps Movement
Introducing Snyk developer-first security into the Terraform Cloud workflow
With the rise in popularity of technologies such as HashiCorp Terraform, Docker, and Kubernetes, developers are writing and maintaining more and more configurations in addition to building the application itself. The growing use of infrastructure as code presents security complexity and the potential for risk that developers often struggle with as their workloads increase and more advanced skills are required.
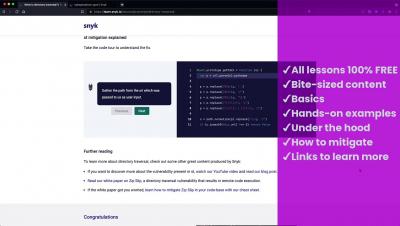
Introducing Snyk Learn
When should a startup call the FBI
Build vs Buy for Start-ups
This is the age-old question faced by so many tech teams: do we build or buy a system we need? TL:DR, Buying can save your engineer time for building the core stack and for the fun experiments needed to determine when to shake up the core stack.