Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
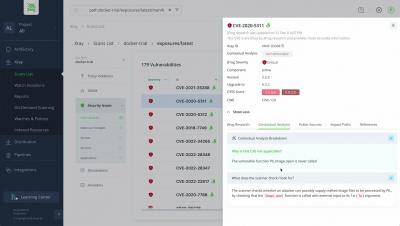
See JFrog Advanced Security in Action
Zero Day Doesn't Mean Zero Hope
#zeroday #security #sca #devops #devsecops #devopssecurity #softwaresupplychain
SnykLaunch recap: Custom Base Image Recommendations
One of the exciting new features discussed at SnykLaunch today was Custom Base Image Recommendations (CBIR). In open beta since late 2022, CBIR is already being used by several organizations. We've been expanding the feature set as we approach general availability to include more flexibility and to incorporate hands-off automation capabilities, allowing users to leverage CBIR in their CI/CD pipelines.
GitOps with Styra DAS and OPA
The practice of infrastructure as code (IaC) has enabled platform teams to control infrastructure using code stored in Git. This enables teams to apply standard development practices like code review and testing to infrastructure management. The practice of GitOps takes this a step further by: Open Policy Agent (OPA), thanks to its Rego policy language, enables organizations to manage their authorization policies as code (PaC).
Why You Should Scan Your Applications in the Repository
If your application development environment is like most, you’re using more code and you’ve accelerated the development of applications and software. That’s great for productivity, but it presents a big challenge for security, as your developers come under increasing pressure to ship code quickly — while also ensuring that their code is secure. They need to find a sweet spot between speed and security, and scanning at the repository level is the way to go. Here’s why.
Recap: Stress-Free Security for Devs and Ops on AWS
Snyk recently hosted a half-day virtual event focused on security for application workloads running on AWS (you can catch it on demand here). The event was broken into six sessions spanning topics like developer challenges in cloud-native AppDev, top vulnerabilities from last year, hands-on workshops with industry-leading technology vendors, and several other subjects that help enable engineering and security teams to build a successful DevSecOps workflow.
Expert Advice on why you should automate server hardening
Enhanced security in JFrog Artifactory using Bytesafe
In the ever-evolving world of software development, secure and efficient package management is crucial to maintaining code integrity and fostering collaboration. While JFrog Artifactory offers a powerful solution for repository management, integrating Bytesafe as an upstream source can further enhance security and collaboration capabilities.
More Security. Less Tool Switching
“Well, yeah, I can give the devs a new security tool, but I can’t make them use it.” I was mid-way through dinner with an old college friend when he dropped this into the conversation. I’d told him I wanted to pick his brain about security issues and tools, but told him no matter what, I wouldn’t start to deliver a pitch. Well, I kept my promise, but I think I must have given my tongue a bruise from biting it.