Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Using Enterprise Data Security to Stay Ahead of Evolving Compliance Standards
As cybersecurity threats and compliance requirements continually evolve, organizations must take a proactive approach to protect their sensitive data. Protegrity’s data protection solution enables businesses to stay ahead of compliance requirements by offering continuous monitoring, encryption, and automated risk assessments, ensuring that security measures are always up-to-date and aligned with the latest regulatory standards.
CMMC Mobile Security: A Guide to Compliance for Enterprise Organizations
Just about every organization works with some amount of sensitive information, but the defense industry’s information is more sensitive than most. That’s why the United States Department of Defense (DoD) created the Cybersecurity Maturity Model Certification (CMMC). This cybersecurity model helps protect controlled data in the defense industry — and, by extension, the military personnel who rely on that data to stay productive and safe.
Securing Snowflake PII: Best Practices for Data Protection
As organizations increasingly rely on cloud data platforms, securing PII (Personally Identifiable Information) has become more critical than ever. Snowflake, a robust cloud-based data warehouse, stores and processes vast amounts of sensitive information. With the rise in data breaches and stringent regulations like GDPR and CCPA, safeguarding PII data in Snowflake is essential to ensure data privacy and compliance.
DORA Compliance Checklist: Essential Steps for Successful Implementation
DORA is an EU-based regulation that is going to be effective from January 17, 2025. It is a digital security framework that works alongside the General Data Protection Regulation (GDPR) to provide strong security protection to financial entities and ICT service providers from cybercrimes. Generally, every financial entity and ICT service provider inside or outside the EU that does business with the EU entities has to comply with DORA.
CMMC 2.0 Explained: What You Must Know For 2025
With the final CMMC rule published, here’s a summary of everything you need to know for your CMMC Level and when. Another step closer. After more than seven years in the making, the US Department of Defense (DoD) finalized a rule establishing the Cybersecurity Maturity Model Certification (CMMC) program and outlining how it will work. The final program rule was published in the Federal Register on 15 October and will go into effect on 16 December.
Top 3 Best Practices for IT Data Security Compliance
For organizations to maintain trust and stay compliant, it’s essential to approach data security as a multi-layered effort that covers some of the top 3 best practices for IT data security compliance, which include Network Security and Access Control, Incident Response Planning, and Employee Awareness and Training.
How to Keep Your CCaaS Solution Secure
A Contact Center as a Service (CCaaS) solution offers your business the flexibility and scalability necessary to manage customer interactions efficiently. However, like most cloud-based systems, your CCaaS platform needs to be successfully secured to protect sensitive information and maintain regulatory compliance-all to ensure the trust of your customers. Ready to secure your CCaaS solution? Here are 7 steps you can take.
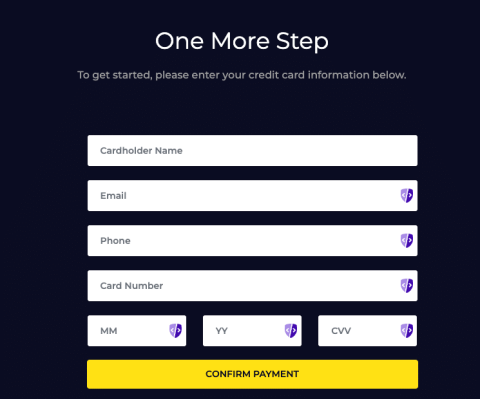
What Is the Cheapest Way to Comply with PCI DSS Requirements 6.4.3 and 11.6.1?
If you’re running a business that takes online credit card payments, you know that you’ve got to become compliant with PCI DSS Requirements 6.4.3 and 11.6.1. Meeting these requirements is crucial for PCI DSS Version 4 Compliance and helps prevent costly data breaches. However, the costs of compliance tools can add up quickly, especially for small businesses. In particular, PCI DSS requirements 6.4.3 and 11.6.1 can seem daunting.
The Vendor's Survival Guide to Security Questionnaires
Depending on who you ask, when the words ‘Security Questionnaire’ are mentioned, opinions will indeed divide. This is usually because not all organizations adopt technology to support the process. In a survey, we conducted with over 150 respondents in the industry, when asked, ‘How does your organization monitor for risks?’ 35.8% answered ‘Manually’.