Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
4 Reasons Cloud-Native Organizations Benefit from Cloud-Native Logging and SIEM
For cloud-native organizations — those begun in the past decade or so — obtaining critical services from other cloud-native companies makes sense. After all, the whole point of being cloud native is to avoid physical infrastructure wherever possible. You want to focus on your business, not managing the systems and infrastructures that support it. That strategy applies to your logging and security information and event management (SIEM) solution, as well.
A Real-World Look at AWS Best Practices: IAM User Accounts
Best practices for securing an AWS environment have been well-documented and generally accepted, such as AWS’s guidance. However, organizations may still find it challenging on how to begin applying this guidance to their specific environments. In this blog series, we’ll analyze anonymized data from Netskope customers that include security settings of 650,000 entities from 1,143 AWS accounts across several hundred organizations.
Cloud Threats Memo: Staggering Statistics About Recent Cloud Misconfigurations
Cloud misconfigurations continue to be a serious concern for organizations, and the list of security incidents caused by the exposure of data from Saas and IaaS applications only continues to grow.
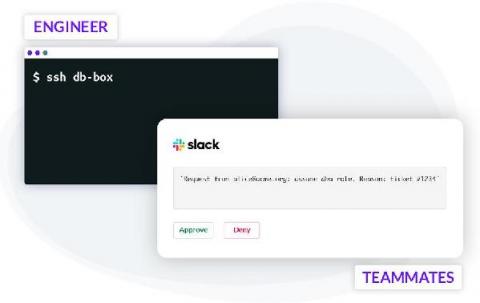
Pull Requests for Infrastructure Access
Making frequent changes to cloud applications running in production is the de-facto standard. To minimize errors, engineers use CI/CD automation, techniques like code reviews, green-blue deployments and others. Git pull requests often serve as a foundational component for triggering code reviews, Slack notifications, and subsequent automation such as testing and deployments. This automated process enforces peer reviews and creates enough visibility to minimize human error.
Navigating Cloud Adoption Myths And Misconceptions
Cloud computing is the vehicle with which modern enterprise organisations drive their digital transformation initiatives. Cloud adoption provides an opportunity for organisations to progress their digital transformation initiatives, scale rapidly and develop their digital service offerings with reduced time and cost overheads, resulting in more agile and efficient working practices and increased value to customers.
Ask SME Anything: What are the major transformations behind SASE architecture?
3 Realistic Ways to Drive Better Networking-Security Team Collaboration
The success of a Secure Access Service Edge (SASE) architecture depends on how well networking and security teams, and the products and services they manage, converge into a shared set of priorities tied to business objectives. Unfortunately, new research from Censuswide confirms this network-security team collaboration is still strained—if not downright combative—at a majority of enterprises.
Secure Session Transfer Between Web Apps on Different Domains
Writing a web application that supports securely logging into a website and managing your credentials is a surprisingly difficult task. You have to develop a way to manage sessions, understand how browsers store state (cookies), learn a cryptographically safe password storing technique (like bcrypt), all the while making sure you mitigate common web security vulnerabilities like XSS and CSRF.