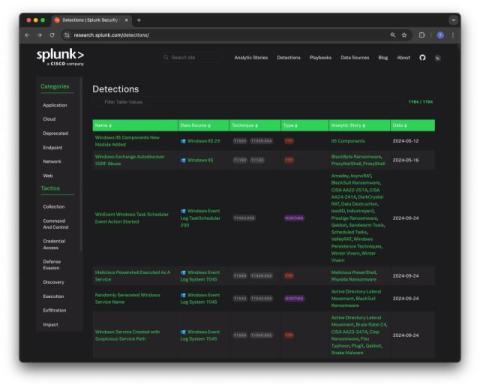
Announcing the General Availability of Splunk Enterprise Security 8.0
At.conf24 we unveiled the private preview of Splunk Enterprise Security 8.0, and the buzz was undeniable. Today, we are thrilled to announce that Splunk Enterprise Security 8.0 is now generally available! This isn’t just another release—it’s a massive leap forward that redefines and revolutionizes security operations. Splunk Enterprise Security 8.0 is the cornerstone of the SOC of the Future.