Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
SnykWeek Boston: Perspectives on developer security adoption
During SnykWeek Boston, Simon Maple (Field CTO, Snyk) led a panel discussion about developer adoption of application security. The panelists included: Want the TL;DR? Here are some of our favorite takeaways: Read on to dive deeper into these illuminating insights around organizing security teams, setting security goals, empowering developers, improving compliance, and much more.
JavaScript Live Panel with Snyk Ambassadors
Hack a vulnerable OWASP Node.js app
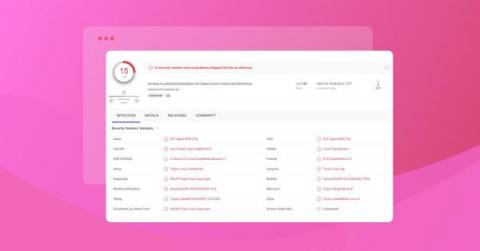
Snyk finds 200+ malicious npm packages, including Cobalt Strike dependency confusion attacks
Snyk recently discovered overt 200 malicious packages in the npm registry. While we acknowledge that vulnerability fatigue is an issue for developers, this article is not about the typical case of typosquatting or random malicious package. This article shares the findings of targeted attacks aimed at businesses and corporations that Snyk was able to detect and share the insights.
How LiveRamp used Snyk to remediate Log4Shell
Like any company that uses web apps or enterprise software built with Java, San Francisco-based LiveRamp was concerned that it had been infected by the Log4Shell zero-day vulnerability within Log4j — the popular open source logging library.
What is DevSecOps? DevSecOps explained in under 7 mins | 2022
Snyk Appoints Adi Sharabani as new Chief Technology Officer
JavaScript Live Hacking
Snyk: Developer Security Platform
The importance of security automation
Security is a critical, if somewhat overwhelming, task for any organization. As products grow and teams expand, the challenge of maintaining a security posture at scale increases as well. This is where automation comes in. The ability to automate security tasks offers obvious benefits such as increased speed, while also driving deeper shifts in a company’s culture and processes.
`npm init JSQuiz` The JS trivia night where you can win prizes!
Snyk Security for Atlassian Bitbucket Cloud Demo
Capture the Flag 101
Stranger Danger: Your JavaScript Attack Surface Just Got Bigger
Detect infrastructure drift and unmanaged resources with Snyk IaC
As a developer, you’re probably using some infrastructure cloud provider. And chances are, you automate parts of your infrastructure using infrastructure as code (IaC), so deployments are repeatable, consistent, easily deployable, and overall, more secure because code makes parameters more visible.
Happy 1st Birthday, Snyk Code!
Snyk Code is turning one! We’ve hit so many milestones in the last 12 months, and today we invite you to look back, celebrate, and peer into the future of code security with us.
This Week in VulnDB - Golang IOT Manager & PHP Zend framework
SurveyMonkey talks with Snyk about developer security during hypergrowth
Many companies look to CISOs or compliance teams to manage security throughout software development. But this practice usually keeps security considerations separate from developers. CISOs can assign security tasks to developers, but if developers aren’t thinking about security regularly, those tasks may be overlooked.
3 Jedi-inspired lessons to level up your JavaScript security
You might think of Star Wars as a movie reserved for geeks, but what if I told you that there are deep life lessons that can be applied to developer security practices? Get your lightsaber ready and prepare to dive into JavaScript security! Star Wars is an epic space-based film series written and directed by George Lucas that often needs no introduction. I’m a fan myself, and personally relate to many of the quotes shared by Jedi Knights in the movie series.
Snyk brings infrastructure as code security to HashiCorp Terraform Cloud
In our mission to make Terraform Cloud workflows more streamlined and secure, we’re excited to announce our new native integration into HashiCorp Terraform Cloud. This integration embeds the security expertise and developer-friendly fixes of Snyk Infrastructure as Code (Snyk IaC) directly into Terraform Cloud, making the Terraform Cloud workflow one of the safest ways to provision and manage public cloud infrastructure.
These aren't the npm packages you're looking for
Over the years, as a developer, I’ve built and deployed many applications through digital agencies, side projects, startups, and freelance work. With time-sensitive deadlines, client expectations, and delivery dates to consider, security wasn’t usually top of mind when npm installing an open source package. This often led to reworking and cleanup on deployments that had let in known vulnerabilities, adding to compounding timelines and client disappointment.
Ignoring vulnerabilities with Snyk
Ignore a vulnerability? That sounds like a paradox. Why would anyone want to ignore a vulnerability? While ignoring security issues should not be your default practice, it is still sometimes necessary. Development and security teams today face vulnerability backlogs consisting of thousands of issues. To maintain rapid development, they must be able to effectively prioritize their work.
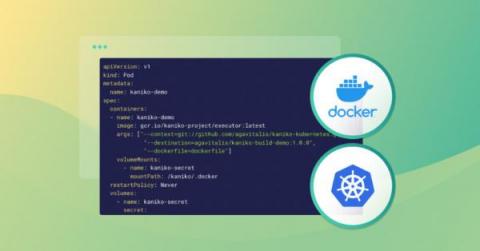
Building Docker images in Kubernetes
Hosting a CI/CD platform on Kubernetes is becoming more common among engineers. This approach saves time through automation, ensures consistent deployments, and makes it easier to monitor and manage microservices. However, building container images in Kubernetes clusters involves some technical hurdles that require workarounds. In this article, we’ll explore some ways to build Docker images in a Kubernetes cluster for CI/CD processes.
Snyk and StackHawk form strategic alliance to equip app teams with modern, developer-first security testing
Application innovation, design, development, quality assurance, and security testing have changed dramatically over the past decade. Engineering teams are leveraging agile development processes, modern cloud platforms, reusable microservices, and extensible APIs, enabling them to shift to more frequent deployments more easily.