Security Awareness Is Dead. Long Live Security Awareness
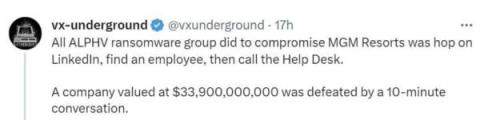
Our actions determine outcomes, not our thoughts, our knowledge, or our intentions. Everyone working in cybersecurity knows that and is all too familiar with statistics like “more than 70% of cyber incidents are facilitated by human action” (in some reports, even up to 95%). Seemingly, security awareness is all about educating people about the dangers that be, but it does not cut to the chase of actually training people to do the right thing.