Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
What you need to know about PCI 4.0: Requirements 5, 6, 7, 8 and 9
In Part 1 of this series, we reviewed the first four sections of the new PCI standards. As we continue our examination of PCI DSS version 4.0, we will consider what organizations will need to do in order to successfully transition and satisfy this update.
Staying Connected with Cloud Exchange: Netskope Cloud Threat Exchange & Digital Shadows Plugin
Many technology professionals have experienced the sense of frustration that occurs when multiple tools in their environment do not play nicely with each other. When technology leaders are making decisions about bringing new tools into their environment, they should be thinking about more than whether the platform is just a shiny new object that adds a new capability to their team.
Why to harden PowerShell and not remove it completely
Stranger Danger: Your Java Attack Surface Just Got Bigger
Get Smarter Network Security Policy Automation
12 Common Pitfalls in EDRM implementation
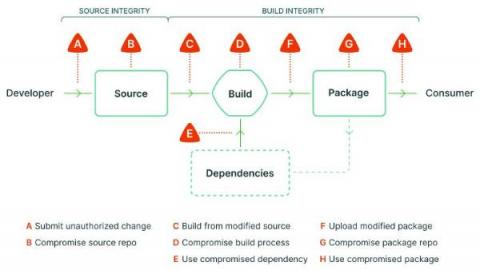
SLSA: A Novel Framework For Secure Software Supply Chains
The software supply chain indicates the formal workflow of how your software moves through the coding stages done by the developers to the final packages for the end-users. When an attacker breaks in between the process and modifies the source code with malicious ones, it is known as an attack on the software supply chain. Software supply chain attacks are challenging to discover and mitigate if you do not have the proper verification and trail-tracking system, especially for large industries.