Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
6 Common Hacking Techniques and How to Avoid Them
According to the recent Verizon Data Breach Investigations report, 45% of breaches featured hacking in 2020. With high-value information such as user credentials and credit card information being stored on personal devices and transmitted freely online, hacking techniques have evolved to become more sophisticated than ever before.
Snyk Customer Story: ActiveCampaign
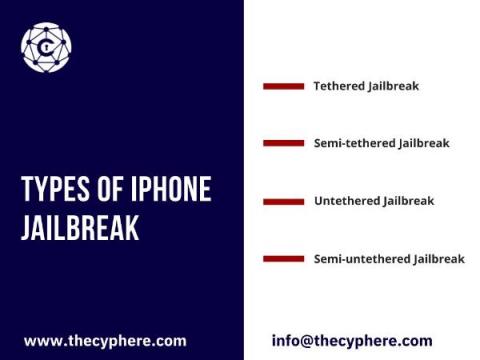
Jailbreaking an iPhone: Should you Jailbreak yours?
The technical term jailbreaking implies that a locked-down electronic device has been changed to remove restrictions and allow the installation of unauthorised software. Although the term contains breaking, it doesn’t involve breaking anything physically.
What is Security as a Service? Advantages and Use of SECaas
Cyber security is a serious concern for businesses in the digital age. It is not uncommon these days to see businesses spending big amounts on security solutions that are difficult to maintain and even more expensive to upgrade. For this reason, security as a service (SECaaS) has gained traction because it allows businesses to outsource their security needs reliably without having to go through the hassle of investing in resources and solutions.
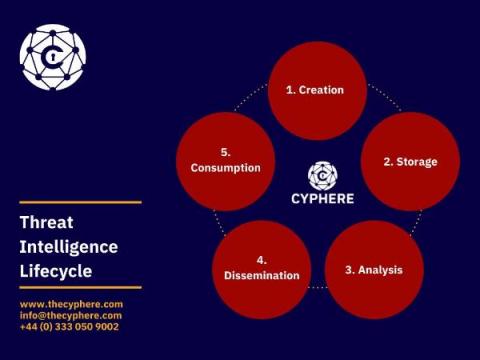
Threat Intelligence: Everything You Need to Know
This blog post will discuss the definition of threat intelligence and different stages of the threat intelligence cycle to help you better understand what happens behind the scenes.
Half a bitcoin to get your data back? How to defeat ransomware attacks.
Law Enforcement Collaboration Has Eastern-European Cybercriminals Questioning Whether There Is A Safe Haven Anymore
Through the active Dark Web research that Trustwave SpiderLabs conducts for its clients, we have observed new communications on various Dark Web forums between Eastern-European cybercriminals. Based on the conversations that we’ve collected, a segment of cybercriminals is now worried that the Russian authorities may be actively hunting them down.
Cloud Threats Memo: Hard Statistics About Poorly Secured Cloud Accounts
Cloud accounts continue to be a valuable target for cybercriminals: not only do the resources of a compromised IaaS environment grant an immediate profit for the attackers, but the same infrastructure also provides a trusted environment to launch attacks against other targets.
10 Ways to Reduce Cybersecurity Risk for Your Organization
Cybersecurity breaches have been on the rise, and it's expected that by 2023, they'll have grown to 15.4 million. While technological advancements have made it easy for organizations to upgrade their security measures, malicious hackers are now using sophisticated tools. This means that in addition to implementing strict cybersecurity policies, you also have to take proactive measures to reduce your cybersecurity risks.