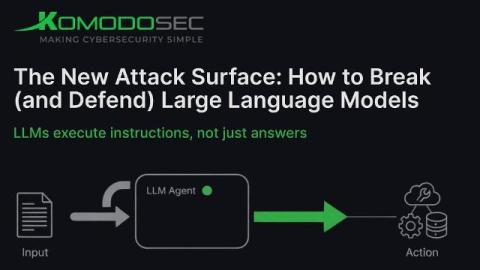
The New Attack Surface: How to Break (and Defend) Large Language Models
Large Language Models now automate customer support, write code, classify emails, generate content, and - disturbingly - execute tasks through plugins and agents. Once an AI can act on your behalf, it becomes part of your operational infrastructure, not a toy. OWASP’s Top-10 for LLM Applications formalized the threat landscape, and quietly confirmed what security researchers have been yelling for two years.