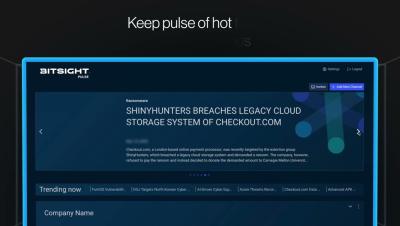
Why Your Attack Surface Is Bigger Than Your SOC Can See | Financial Cyber Risk Explained
Your organization’s attack surface doesn’t stop at the network—and in financial services, that reality can’t be ignored. In this clip, Dov Lerner explains why even companies with strong internal security programs remain vulnerable when attackers target customers through phishing and account takeover schemes.