Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
How Businesses Can Stay Safe From Undetected Cyber Attacks
Lockbit Ransomware Gang - Longevity or Downfall?
High-profile ransomware attacks against large businesses and governments have become increasingly popular. They typically occupy news headlines on a monthly basis. As of writing, the most recent, high-profile attack was launched against Porsche, South Africa, where IT systems and some backups were impacted by ransomware from an unknown attacker. The gangs that perpetrate these attacks typically have carefully-crafted, large public personas and engage in significant posturing.
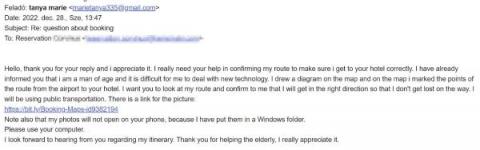
Checking In For Disaster: Credential Phishing Campaign Targeting the Hospitality Industry
Since late December 2022, the ThreatSpike team has noticed a significant rise in highly targeted phishing campaigns aimed at the hospitality sector, which distribute infostealer malware. The threat actors (TAs) are primarily targeting front desk and reception staff, as they are responsible for handling customer queries via a generic email that can easily be found on the company website.
Redline Infostealer Analysis (Part 2)
Redline infostealer gathers information and steals high value data from an infected machine. The Redline infostealer is considered one of the most dangerous malware currently being used in the wild and has been used in countless trojanized software, applications, games and cracked software. In addition to data exfiltration, Redline also has the capability to connect to a command and control (C2) server to download, upload files as well as perform remote commands.
ThreatSpike Red Disrupts Elite Cybersecurity Market with Revolutionary Offensive Cybersecurity Service for all Businesses
ThreatSpike
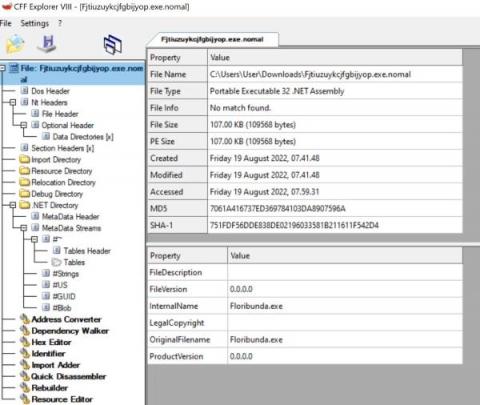
Redline Infostealer Analysis (Part 1)
This blog post will provide an analysis of the malicious Redline Infostealer payloads which have been taken from a real life malware incident, responded to and triaged by the ThreatSpike SOC team. This analysis will be broken down to demonstrate, describe and explain the various stages of the attack chain.
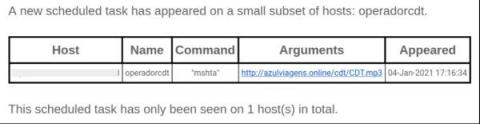
The Tactics and Techniques of Mid-Tier Adversaries, Described in 3 Attacks
When it comes to cyber security, attackers seem to be classified as terrifying Advanced Persistent Threats (APTs) or trivialised as Script Kiddies. However, more often than not, the attackers that are actually faced lie somewhere in the middle; the not-so-advanced yet somewhat-persistent threat. Their attacks are often detected but can be difficult to unravel. Their Tactics, Techniques and Procedures do not include any zero-days, but still they manage to show ingenuity.
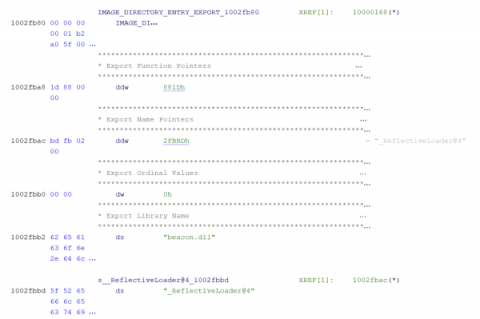
Dissecting The Cobalt Strike Beacon
In a previous article, we introduced a piece of malware that ThreatSpike detected in December 2020, moving laterally between hosts. The attack consisted of two components: A text editor repurposed as a launcher for the actual payload, identified as Cobalt Strike’s Beacon.