Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
The JFrog Platform Delivered 393% ROI
I’m excited to share the findings of a Forrester Consulting Total Economic Impact™ (TEI) study, a recently commissioned study conducted by Forrester Consulting on behalf of JFrog, which examines the potential return on investment (ROI) that organizations may realize by deploying the JFrog Software Supply Chain Platform. Software has become the critical infrastructure of our daily lives.
Trusting your Software Supply Chain Security with DevOps Agility
From zero to breach in seconds: Why you need to focus on software supply chain security now
The RSA Conference 2023 addressed several key issues and trends in the cybersecurity industry. Generative AI was a key topic of discussion, with attendees, executives and policymakers seeing its potential in both offense and defense in the cybersecurity arms race.
How a software supply chain platform streamlines DevOps best practices
Today’s software developers are tasked with a lot more than just coding. To keep up with the fast-paced software-driven economy, they need to focus on automation, collaboration, security, distribution, data analysis, and agility to ensure quality builds and get releases to customers quickly and securely. DevOps and security professionals need a centralized system of records that provides visibility across the business.
Curating Open source Libraries on JFrog Platform, part II.
New .NET Malware "WhiteSnake" Targets Python Developers, Uses Tor for C&C Communication
The JFrog Security Research team recently discovered a new malware payload in the PyPI repository, written in C#. This is uncommon since PyPI is primarily a repository for Python packages, and its codebase consists mostly of Python code, or natively compiled libraries used by Python programs. This finding raised our concerns about the potential for cross-language malware attacks.
Software Supply Chain Security at RSA Conference 2023
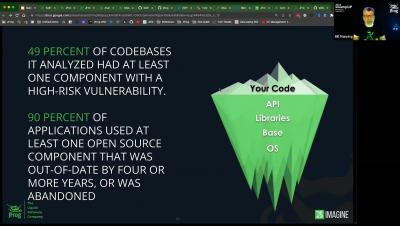
The risk of supply chain attacks increases as more companies rely on third-party vendors and suppliers for critical services and products. Supply chain attacks have become increasingly prominent in recent years. In 2022, for instance, supply chain attacks surpassed the number of malware-based attacks by 40%.
Secrets Detection JFrog Security Workshop
Analyzing Impala Stealer - Payload of the first NuGet attack campaign
In this blog post, we’ll provide a detailed analysis of a malicious payload we’ve dubbed “Impala Stealer”, a custom crypto stealer which was used as the payload for the NuGet malicious packages campaign we’ve exposed in our previous post. The sophisticated campaign targeted.NET developers via NuGet malicious packages, and the JFrog Security team was able to detect and report it as part of our regular activity of exposing supply chain attacks.