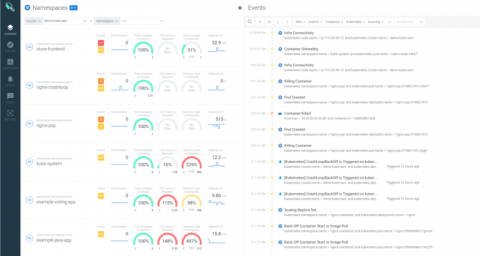
Sysdig extends security across all AWS container services
Cloud teams are increasingly adopting AWS container services to deliver applications faster at scale. Along with the roll out of cloud native architectures with containers and orchestration, what’s needed to stay on top of the security, performance and health of applications and infrastructure has shifted. At Sysdig, we’ve worked with Amazon to provide tools and integrations that help secure your Cloud Native workloads deployed across all AWS container services.