Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
A Look Back at the Executive Order on Cybersecurity
It has officially been one year since the release of the Biden administration’s Executive Order on Cybersecurity, which outlines security requirements for software vendors selling software to the U.S. government. These requirements include security testing in the development process and a software bill of materials for the open-source libraries in use so that known vulnerabilities are disclosed and able to be tracked in the future, among other things.
What Is Software Supply Chain Security?
Most software today isn’t developed entirely from scratch. Instead, developers rely on a range of third-party resources to create their applications. By using pre-built libraries, developers don’t need to reinvent the wheel. They can use what already exists and spend time on proprietary code, helping to differentiate their software, finish projects quicker, reduce costs, and stay competitive. These third-party libraries make up part of the software supply chain.
Coded for Safety
Ready to secure government applications? Start with Zero Trust. Trust is the foundation of successful relationships. We want to trust our friends, companies, government, etc., and be trusted in return. But, sometimes mistrust better serves us. A few years ago, the cyber world adopted an approach to security known as trust-but-verify. A simplistic approach, it delivered innovative digital services to consumers – securely and efficiently.
Bridging The Needs Of Security And Development Teams, Veracode Unveils Next-generation Software Security Platform
Official Close of TA Investment Sparks Next Step of Veracode Journey
Recently I shared with you our excitement about our agreement with TA Associates (TA) to make a significant growth investment in Veracode. I am pleased to share that the deal is now closed, opening up a tremendous new chapter in Veracode’s journey.
What makes an Application Security Champion | Evan Gertis
How to generate a Software Bill of Materials (SBOM) using Veracode Software Composition Analysis
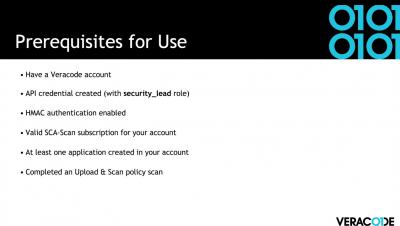
How to Generate an SBOM in Veracode SCA
Emerging government regulations have driven the advancement of standards for securing software supply chains. The production of a Software Bill of Materials (SBOM) in a standard format is an increasing audit and compliance need for large organizations.