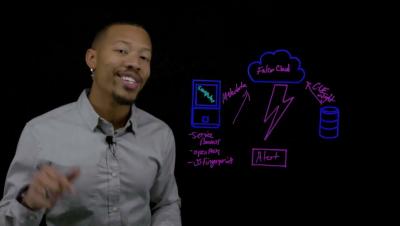
Lightboard Lab: Closing the Valley of Visibility in Network Vulnerability Assessment
Network Vulnerability Assessment is often treated as a point-in-time exercise—but real environments don’t stand still. Between long scan cycles, two things are constantly changing: network devices drift as configurations and versions evolve, and the world around them shifts as new vulnerabilities are disclosed.