Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Exploiting, Mitigating, and Detecting CVE-2021-44228: Log4j Remote Code Execution (RCE)
A new critical vulnerability has been found in log4j, a widely-used open-source utility used to generate logs inside java applications. The vulnerability CVE-2021-44228, also known as Log4Shell, permits a Remote Code Execution (RCE) allowing the attackers to execute arbitrary code on the host. The log4j utility is popular and used by a huge number of applications and companies, including the famous game Minecraft.
Visibility and Security for GKE Autopilot
GKE Autopilot from Google Cloud is a mode of operation in Google Kubernetes Engine (GKE) designed to simplify working with Kubernetes in the cloud. Pairing secure DevOps practices with GKE Autopilot will help you and your teams ensure the security, compliance, and performance of your workloads and applications. Sysdig has collaborated with Google Cloud to enable visibility and security for GKE Autopilot and your containers.
Mitigating log4j with Runtime-based Kubernetes Network Policies
A critical vulnerability, CVE-2021-44228 known as “log4shell,” in Apache’s log4j was revealed on December 10th, 2021, and has already seen wide exploitation around the Internet. Previously, we discussed the vulnerability and how to find it in your images using Sysdig Scanning reports. In a perfect world, patching would be quick, easy, and completed without any issues.
Critical vulnerability in log4j, a widely used logging library
Security researchers recently disclosed the vulnerability CVE-2021-44228 in Apache’s log4j, which is a common Java-based library used for logging purposes. Popular projects, such as Struts2, Kafka, and Solr make use of log4j. The vulnerability was announced on Twitter, with a link to a github commit which shows the issue being fixed. Proof-of-concept code was also released to github which shows that the vulnerability is trivial to exploit.
Threat news: TeamTNT stealing credentials using EC2 Instance Metadata
The Sysdig Threat Research Team has detected an attack that can be attributed to the TeamTNT. The initial target was a Kubernetes pod exposed outside the network. Once access was gained, the malware attempted to steal AWS credentials using the EC2 instance metadata. TeamTNT is a threat actor that conducts large-scale attacks against virtual and cloud solutions, like Kubernetes and Docker.
Run confidently with secure DevOps
Hands-On Muhstik Botnet: crypto-mining attacks targeting Kubernetes
Malware is continuously mutating, targeting new services and platforms. The Sysdig Security Research team has identified the famous Muhstik Botnet with new behavior, attacking a Kubernetes Pod with the plan to control the Pod and mine cryptocurrency. A WordPress Kubernetes Pod was compromised by the Muhstik worm and added to the botnet. On the Pod has been deployed and executed various types of crypto miners, like xmra64andxmrig64.
Getting started with runtime security and Falco
Discover how to get started with Falco to overcome the challenges of implementing runtime security for cloud-native workloads. If you are adopting containers and cloud, you are probably enjoying benefits like automated deployments and easier scalability. However, you may also find that when it comes to security, this is a whole new world with new rules, and traditional security tools struggle to keep up. As a new paradigm, cloud-native environments need new cloud-native tools.
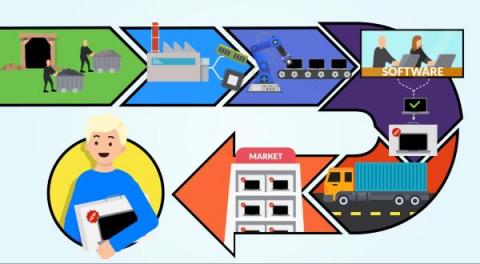
Secure software supply chain: why every link matters
The new threats in software development are not only related to the specific company itself. The whole software supply chain is a target for attackers and it is really important to make sure that we put all our effort into securing each link because if one fails, everything will be affected. Supply chain activities include each step of the transformation of raw materials, components, and resources into a completed product, and its delivery to the end customer.