XRP supply chain attack: Official NPM package infected with crypto stealing backdoor
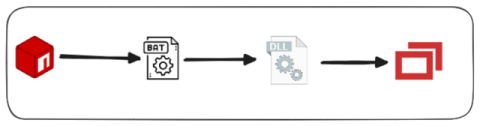
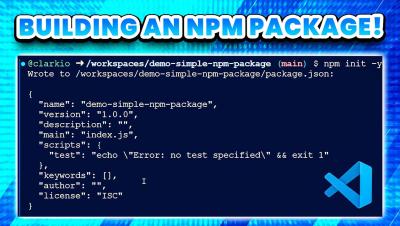
At 21 Apr, 20:53 GMT+0, our system, Aikido Intel started to alert us to five new package version of the xrpl package. It is the official SDK for the XRP Ledger, with more than 140.000 weekly downloads. We quickly confirmed the official XPRL (Ripple) NPM package was compromised by sophisticated attackers who put in a backdoor to steal cryptocurrency private keys and gain access to cryptocurrency wallets.