Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
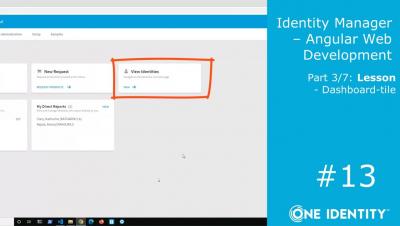
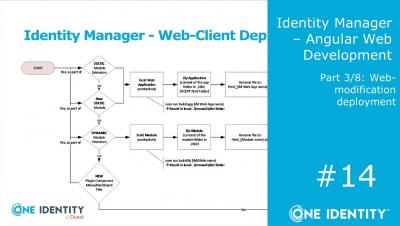
Identity Manager | Angular Web Development #14 | Modifying the Standard Web Portal #8
See Falcon Identity Protection in Action
Falcon Identity Protection Honeytokens: Demo Drill Down
Falcon Identity Protection Risk-based Conditional Access: Demo Drill Down
The Case for Single-Tenant SaaS for IGA
More and more organizations are moving towards a cloud-first strategy where they look to move their on-premises applications to SaaS offerings. This is especially true for customers looking to streamline their on-premises Identity Governance and Administration (IGA) application via a move to the Cloud.
3 Types of Privileged Accounts to Secure in a Transforming Enterprise
For security teams managing their enterprises’ privileged access management (PAM) programs, times have changed and what’s considered a privileged or high-risk account has drastically shifted. In turn, the way organizations not only manage privilege, but comprehensively secure it, must also shift. Historically, organizations have managed their PAM programs by vaulting and rotating credentials on privileged accounts.
EP 34 - How to Catch a Malicious Insider w/ Eric O'Neill
Today’s episode of Trust Issues focuses on spycatching! Eric O’Neill, a former FBI counterintelligence operative and current national security strategist, joins host David Puner to discuss his legendary undercover mission to capture Robert Hanssen, one of the most notorious and damaging spies in U.S. history.
NVMe: New Vulnerabilities Made Easy
As vulnerability researchers, our primary mission is to find as many vulnerabilities as possible with the highest severity as possible. Finding vulnerabilities is usually challenging. But could there be a way, in some cases, to reach the same results with less effort?