Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
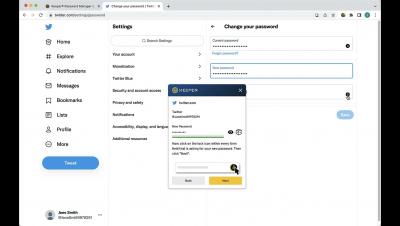
Changing Your Passwords
Untangle the Secrets of your JavaScript Dependencies
Making the Vendor Questionnaire Process More Efficient (in 2022)
Vendor security questionnaires are frustrating, both to the organizations sending them and the vendors receiving them. While these frustrations remain unaddressed, they will only continue to impede the efficiency of vendor risk management programs. Fortunately, suffering through security assessments isn’t an unavoidable by-product of a Vendor Risk Management program. With the correct strategies, you can streamline the entire assessment questionnaire lifecycle. Read on to learn how.
Compliance Guide: NIST CSF and the Healthcare Industry
Today’s threat landscape is driven by digital transformation and the outsourcing of critical operations to third-party vendors. Cybercriminals’ high demand for sensitive data paired with a historical lack of cybersecurity investment across the industry is cause for concern. Healthcare organizations recognize they have the choice to either increase their cyber spending or inevitably fall victim to a costly data breach. However, investing in cybersecurity solutions alone isn’t enough.
Interpreting the Key Points of The 2022 IBM i Marketplace Survey Results
This year marks the eighth edition of the popular IBM i Marketplace Survey Results. Each year, HelpSystems collects data about how companies utilize the IBM i platform and the IT enterprises it helps. Year after year, the survey has started to demonstrate long-term directions that provide useful information about the future of this entrusted technology.
A 5 Step Checklist for Complying with PCI DSS 4.0
In March 2022, the Payment Card Industry Data Security Standard (PCI DSS) was updated with a number of new and modified requirements. Since their last update in 2018, there has been a rapid increase in the use of cloud technologies, contactless payments have become the norm, and the COVID-19 pandemic spurred a massive growth in e-commerce and online payments.
Security Operations Center (SOC) - A Worthful Investment for an Organization
Modern innovations change the face of the modern digital world. Meanwhile, the risk of cyberattacks remains a disaster for every organization. A platform effectively uses humans, technology, and resources to secure organizational functions. It works continuously round the clock to eradicate and rectify all sorts of attacks. Organizations adopt such platform depending on their level of competency in providing security services to their customers.