Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Managed Detection and Response Buyer's Guide - Key Takeaways
NCSC Annual Review 2022
After reviewing the NCSC Annual Review for 2022, we discuss our 5 key takeaways and give our thoughts on the topic.
How Small Businesses Can Improve Their Cybersecurity
The need for cybersecurity in small and midsize businesses (SMBs) has never been more crucial. Any organization can suffer catastrophic effects from cyberattacks, but small businesses are particularly vulnerable. Unprepared small firms may experience tremendous financial consequences as well as damage to their reputation, productivity, staff morale and much more when a cyberattack occurs. When establishing cybersecurity processes and strategies, it is crucial to understand the risks.
Ransomware Attacks and Remediation Strategies for Financial Institutions
Believe it or not, the Financial Services industry has one of the slowest vulnerability remediation rates, with a median of 426 days. “Financial regulators can no longer rely on static, point-in-time assessments to understand the cybersecurity risks posed to the financial system,” said Sachin Bansal, SecurityScorecard’s Chief Business and Legal Officer, in a recent BusinessWire article. “Continuous monitoring tools must be a part of every regulator's toolbox.”
The Benefits of Negative Testing in Software Testing
In software testing, negative testing refers to the practice of feeding a system with unexpected or invalid inputs. Given an input field that accepts numeric values from 0-100, positive tests would assess if the application does what it's supposed to do, given input values such as "1", "2" or "99".
The Current State of Cybersecurity Compliance
We can do better: The tech industry and its response to data breaches
My colleague, 1Password Senior Security Specialist (and all round stand-up guy) Chris Butler, and I recently chatted about a trend that’s emerged over the past few years: attempts to capitalize on cybersecurity incidents through self-promotion.
5 Reasons to Start Pseudonymizing Personal Data in Your Organization
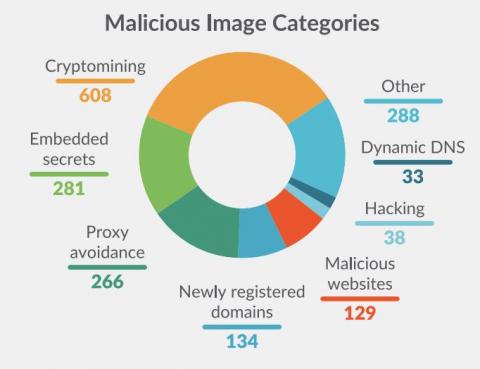
Analysis on Docker Hub malicious images: Attacks through public container images
Supply Chain attacks are not new, but this past year they received much more attention due to high profile vulnerabilities in popular dependencies. Generally, the focus has been on the dependency attack vector. This is when source code of a dependency or product is modified by a malicious actor in order to compromise anyone who uses it in their own software.