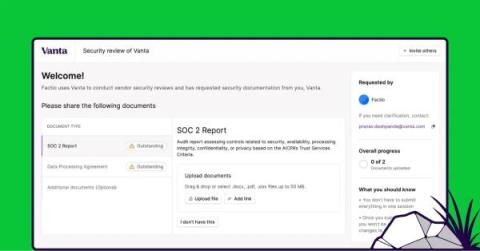
Reinvent the way you partner with your supply chain to fix and mitigate security issues
It’s that time of the year again, 2024 planning. Security and third-party risk management leaders are scrambling to prioritize their initiatives for the coming year, advocate for more resources, and report on their progress over the past year. When only 16% of organizations report that they effectively manage third-party risk, the new year provides a blank slate to introduce new efficiencies to existing processes.