Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Jailbreaking an iPhone: Should you Jailbreak yours?
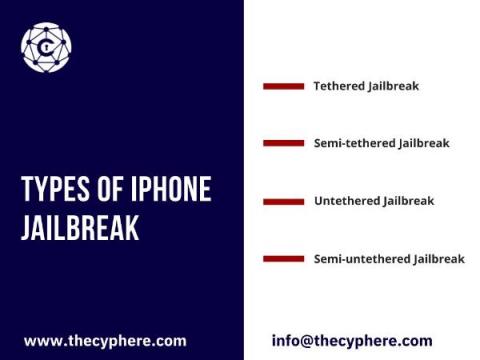
The technical term jailbreaking implies that a locked-down electronic device has been changed to remove restrictions and allow the installation of unauthorised software. Although the term contains breaking, it doesn’t involve breaking anything physically.
Predictions 2022: Work-from-anywhere Marks the Beginning of the End of On-premises Security
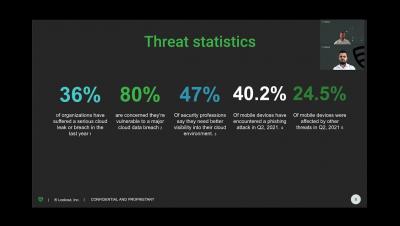
A decade ago, many were reluctant to move to the cloud. Many felt like they would have to relinquish controls they had within their perimeters. That sentiment has since reversed, where organizations have become more comfortable with cloud technology. The newest concern is about corporate data leaving the cloud, especially as employees expect to work from anywhere. Software-as-a-service (SaaS) applications have enabled people to stay productive from anywhere, but have also amplified security gaps.
How to protect data loss from productivity tools
Secure Your Infrastructure From Stealthy Cyber Threats
The "Just Because" of Zero Trust | OptivCon 2021 Interview
Prepare for the next phase of work from anywhere security
Achieve Enhanced Cloud Security with DLP
Zero Trust isn't a Buzzword
Achieving Zero Trust? One Size Does Not Fit All
More than a year of near-universal remote work has proven that many of us can reliably stay productive from anywhere — whether it be from home, co-working spaces or otherwise. Businesses have caught wind of this, and according to IDC, 60% of them will continue with remote work or implement a hybrid model even after they reopen their offices again. This calls for a paradigm shift in the way we conduct cybersecurity.