Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Why you need to pay attention to mobile app security
Aside from executing physical attacks on servers, hardware or people, there are three main access points where criminals can break into systems: web, mobile and API. In this post, we’ll focus on mobile security, an area increasingly being exploited due to a sharp rise in mobile device use over the course of the pandemic.
CASB Solution
Critical Requirements for Mobile Security
0:00 Opening
6:06 What is Zero Trust?
11:48 Zero Trust workforce on mobile devices
14:57 Enabling Phishing protection on mobile
26:10 Vulnerability management for devices and applications
33:05 Ability to hunt for threats on mobile
43:45 Critical capabilities for comprhensive security
45:20 Q&A
Interview with a Hacker How are Attackers Targeting Mobile Devices
Apps Under Attack - What You Need To Know
0:00 Opening
4:50 What mobile threats are out there?
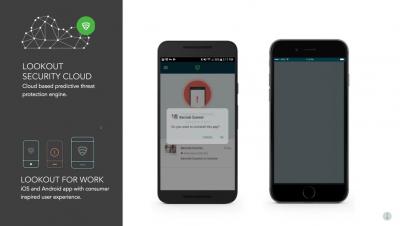
11:20 Lookout Mobile App solution
13:35 Lookout Threat Discoveries
23:57 Banking Trojans
25:54 Strandhogg
28:40 Detecting Malware
35:36 How does Lookout protect mobile?
Critical Capabilities for Mobile Vulnerability Management
Protecting Mobile Point of Sale and Financial Apps From Cyber Breaches
White Box Cryptography- Everything You Need to Know
In the world of heinous and sophisticated crimes, cryptography is the next-gen solution needed to resolve the concern. Whitebox cryptography combines encryption and obfuscation methods to embed secret keys in application code. The aim is to combine code and key in such a way that an attacker cannot distinguish between the two and the new "white-box" program can be safely executed in an insecure environment.