Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Zero Trust - Replacing Depth with Logic. Identity & Access Management eSummit 2022
In a hybrid work setup, workers should be able to authenticate themselves in the virtual environment securely. However, identity theft and technologies like deep fakes ensure that securing identities remains a major challenge. Organizations want to ensure their identities are safe and hack-proof. Join industry leading practitioners and experts to learn how to protect identities.
Setting up Teleport (tsh) on Mac
https://goteleport.com/docs/installation/#macos
0:00 Introduction
2:00 tsh login
2:56 tsh ls
3:35 tsh ssh
3:58 tsh help
Identity-Based Data Security on AWS
Speakers: Dave Cole, CEO of Open Raven Ev Kontsevoy, CEO of @Teleport Modern data drives business value. But the speed with which it is created and accessed across a global AWS footprint increases risk considerably. The old ways of securing data – VPNs, shared credentials stored in a secure vault, offsite backups – are no longer sufficient and don't work at cloud-scale. Join Teleport CEO Ev Kontsevoy and Open Raven CEO Dave Cole as they present a practical view of modern data security in two parts.
How to enable WebAuthn based second-factor authentication in Teleport.
This video shows how to enable WebAuthn based second-factor authentication in Teleport. Teleport implements the Web Authentication API or WebAuthn, which is a W3C specification for passwordless authentication using public-key cryptography.
What is a BISO? How a BISO can help accelerate Fintech innovation.
For this 15th episode of Access Control Podcast, a podcast providing practical security advice for startups, Developer Relations Engineer at Teleport Ben Arent chats with Alyssa Miller. Alyssa is a seasoned hacker and highly experienced security executive. Alyssa began her career programming for a Wisconsin-based provider of financial software and services. Later moving into a leadership role within the ethical hacking team, conducting pen tests and app assessments. This was followed by working in consulting, which provided a unique perspective on the challenges of the security industry, and then working across multiple organizations and high-level executives to address security at a strategic level.
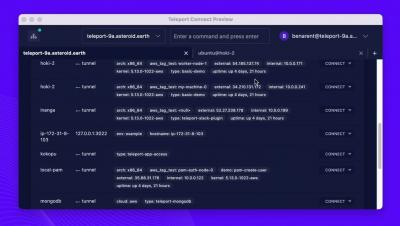
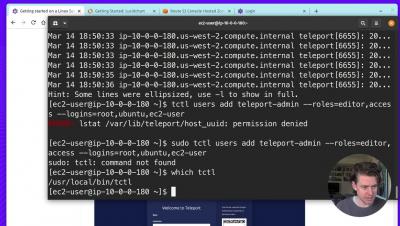
Getting started with Teleport 9
0:00 Introduction
1:10 Install Teleport on Root Cluster
5:33 DNS
6:36 Configure Teleport
10:17 Create Teleport User
14:09 Have Fun with Teleport
Lessons From Billions of Breached Records by Troy Hunt of https://haveibeenpwned.com
Security flaws, hackers and data breaches are the new normal. It’s not just those of us in the industry facing these foes every single day; it’s everyone. Whether you’re online or offline, you simply cannot exist today without your personal information being digitized in systems which are often left vulnerable and exploited at the whim of attackers. But who are these people — the ones who seek to break through our defenses and exploit our data? And how are they continually so effective at doing so, despite our best efforts?