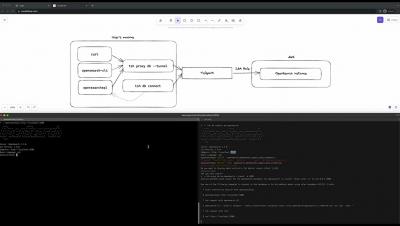
Teleport 13: Automatic agent updates, Simplified AWS setup, Light theme, and more.
Once again, it’s time for everyone’s favorite announcement: a brand new Teleport release! This release marks version 13 of Teleport and is packed with features, including a UI makeover, performance improvements, a few exciting previews, and so much more. Let’s dive in! Watch this episode recording with Ben Arent, Teleport’s Director of Developer Relations, as he discusses what’s new in Teleport 13.