Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Latest News
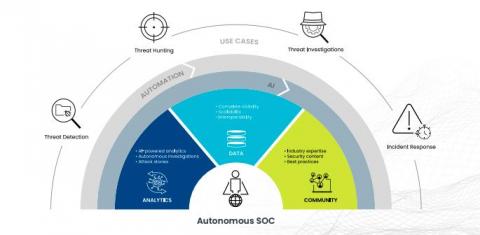
Emerging Technologies and Evolving Analysts Are Giving Rise to the Autonomous SOC
Fueled by the need to detect new, emerging threats while supplying meaningful feedback upstream to anticipate and prevent future ones, the modern SOC is the engine that protects organizations worldwide. The heart of that engine is common to all SOCs since they debuted more than a decade ago: people.
How to Use SIEM Tools in the Modern World
In our highly connected world, organizations of all sizes need to be alert to the risk of cyberattacks. The genuine threats to today’s enterprises include data leaks, ransomware, and theft of commercial secrets or funds, with the potential for severe financial and reputational damage. Investing in tools to monitor your systems and alert you to suspicious activity as early as possible is vital for strengthening your security posture.
6 cybersecurity must-haves for innovative public sector leaders
ThoughtLab’s newly released cybersecurity benchmark study revealed that cybersecurity is at a critical inflection point across industries.
Public Sector Demand for Devo Solutions Leads to New Partnerships & Contracts
Following our February announcement that Devo has been designated as FedRAMP “In-Process,” I’m excited to report that our public sector momentum continues in other key areas. Here are some recent highlights: All of this momentum and growth is an affirmation of the excellence of the Devo Platform and the exceptional quality of our success services to support them. And it also demonstrates Devo’s long-term commitment to serving our customers and partners in the public sector.
A peek behind the BPFDoor
Threats knock on your door all the time. In this research piece, we explore BPFDoor — a backdoor payload specifically crafted for Linux in order to gain re-entry into a previously or actively compromised target environment. This payload has been observed across systems for five years, suggesting that the threat actors responsible for operating the malware have been around for some time and have likely operated undetected in many environments.
Is your penetration testing weak? Catch hackers at your backdoor with Sumo Logic
Top Security Information and Event Management Use Cases
Cyber security threats and measures mandated by regulations require an advanced security solution for organizations. Many reasons, such as false positives, difficulty in budget control, vulnerable protocols, and misconfigurations, can be confusing when choosing the right security solution. In order to get rid of all these concerns, security information and event management (SIEM) solutions come to the fore as solid and centralized security platforms.
Elastic and Tines partner to detect security threats and reduce mean time to respond
Today, we’re happy to announce that Elastic and Tines are partnering to help our joint users detect security threats and reduce mean time to respond. Many of the world’s best security teams rely on the power of Elastic’s high-speed, cloud-scale detection, prevention, and response capabilities to investigate and contain potential security threats within their environments.
Shell Evasion: An Insider Threat
Cybersecurity strategies within cloud environments are often seen as a complicated landscape with rapidly developing technologies, architectures, and terms. Simultaneously, there are continuously motivated individuals and groups trying to utilize vulnerabilities for illicit uses such as to increase access to the data, install malware, disrupt services, and more.