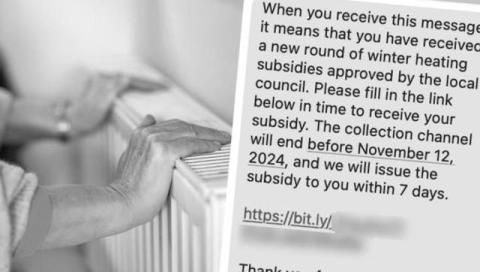
Identity Fraud and the Cost of Living Crisis: New Challenges for 2024
Fraud is a rampant threat to individuals and organizations worldwide and across all sectors. In order to protect against the dangers of fraud in its many forms, it is vital to stay in the loop on the latest fraud trends and the threat landscape. The Fraudscape 2024 report from Cifas, the UK’s Fraud Prevention Community, is an effort to share this information to help prevent fraud.