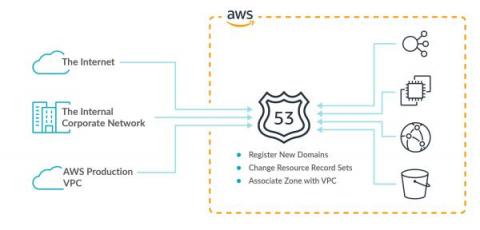
Detecting suspicious activity on AWS using cloud logs
AWS offers a large spectrum of services and compute. The “shared responsibility” model in cloud presents a simplified structure of organization responsibilities and cloud provider responsibilities. Generally, identity and access management (IAM), applications, and data form the dividing line, but lines blur depending on the given cloud service the organization is consuming. This is true of all cloud providers, including the AWS Shared Responsibility Model.