Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
The latest News and Information on Data Security including privacy, protection, and encryption.
What is Lateral Movement in cyber security? Different ways to prevent it
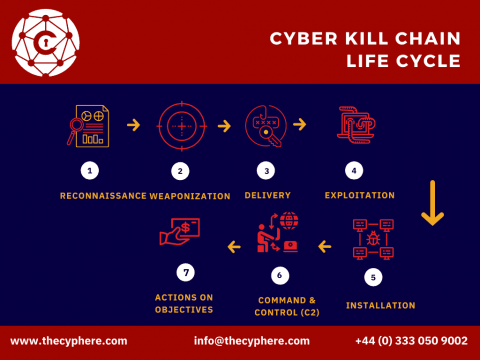
Lateral movement refers to the techniques that a cyber attacker uses. Once getting access to a corporate network, the attackers don’t stop there. They move around throughout the entire network, owning more computers and user accounts while exfiltrating data at the same time. They escalate their privileges to gain access to higher permissions and eventually access more confidential, critical and sensitive data.
5 Things We Learned from The Definitive Guide to Data Loss Prevention (DLP)
In the context of hybrid work, the threat of data loss is rampant. Cybersecurity systems that were once designed to operate within the confines of a network perimeter have become obsolete, with employees using various devices, networks, and applications to get their work done. As such, it’s easier than ever for companies to be vulnerable to the loss of sensitive data. So, what’s the solution? Recently, Digital Guardian published The Definitive Guide to DLP: 2021 Hybrid Work Edition.
Improve Your Cloud Data Protection Through Protegrity's S3 AWS Marketplace Integrations
What is Data Hygiene and Why Is It Important
Many organizations are already cashing in on the promise of big data, hailed as the world’s most valuable resource. However, this crude resource requires refining in the form of data hygiene. Data errors and inconsistencies cost companies millions of dollars a year. Businesses that aren’t able to implement the tools, strategies, and training required often find big data to be more of an obstacle than an advantage.
NC Protect advanced data protection for secure government, defense & supply chain collaboration
Protegrity: Solutions for the Future of Data Privacy and Protection
Introducing Kojensi SaaS v2.0 with New Export Control Material Capability for ITAR
Cyber Hygiene Key Principles and Best Practices
Ransomware and other cyber attacks are getting more expensive every year. IBM’s recent report found that the average cost of a breach increased 2.6% from $4.24 million in 2021 to $4.35 million in 2022 — and the year isn’t over yet. Too often, data breaches are the result of routine lapses.
How to reduce your exposure & secure your data in the cloud in 5 quick ways
More companies are switching from on-premises systems to public cloud services, ensuring long-term growth and digital resilience. But as their implementations grow, they begin to realize that their exposure to cyberattacks and other risks grows as well. Cybersecurity is an essential practice for successful businesses. Adapting to business growth is a good problem to have, but without an eye on cloud security, that growth could cost you in the long run.