Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Cybersecurity at the Tactical Level: The Importance of StateRAMP
Here in the United States, we often focus on the cybersecurity readiness of the federal government. The reality is that state and local government departments are just as, if not more vulnerable to cyber attacks. Nearly one quarter of their employees use personal devices for work, where security teams have little visibility, enabling threat actors to execute phishing and other malicious activities. These risks will only continue to grow as in-person services continue remotely.
CrowdStrike Store - Falcon FileVantage
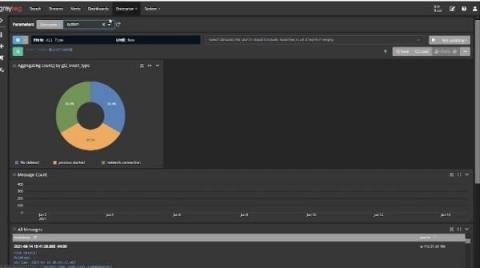
Using Log Management for Compliance
It’s that time of the year again. The annual and dreaded IT and security audit is ramping up. You just received the documentation list and need to pull everything together. You have too much real work to do, but you need to prove your compliance posture to this outsider. Using log management for compliance monitoring and documentation can make audits less stressful and time-consuming.
Securing cloud infrastructure for PCI review
The PCI certification process is quite comprehensive and relates to infrastructure, software and employee access to systems, in particular to datasets and the way that they are accessed. These checks are critical not only to the wider payments industry but also to create a level of trust with users knowing their data is protected. The PCI compliance process is a number of checks, usually by an accredited third party, to ensure that secure data handling processes are in place.
CMMC Town Hall With Bill Walter, DHG & Eric Crusius, Holland & Knight | 3/2/22 | NeoSystems
The data ditch: a toolkit to identify and escape it
The dreaded data ditch. You might not even know your organization is stuck in it – the company might still be acting on gut feel as opposed to relying on data, the data you have might be ungoverned and inaccurate, or you’re waiting weeks, even months, for your teams to glean useful insights. You’re not alone. Data leaders like yourself keep falling into the data ditch.
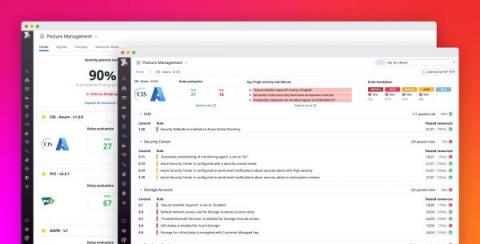
Monitor the security and compliance posture of your Azure environment with Datadog
Governance, risk, and compliance (GRC) management presents some unique challenges for organizations that deploy a myriad of cloud resources, services, and accounts. Simple misconfigurations in any of these assets can lead to a serious data breach, and compliance issues become even more prevalent as organizations try to inventory and manage assets across multiple cloud platforms and security and auditing tools.