What is Information Security?
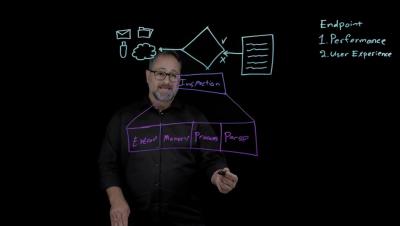
Unlock the secrets of Information Security (Infosec)! In today's digital age, protecting your data is paramount. This video breaks down what Infosec truly is, going beyond just digital threats to cover all forms of information – from physical files to conversations.