Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
CVE-2023-41265, CVE-2023-41266 & CVE-2023-48365: Multiple Vulnerabilities in Qlik Sense Enterprise Actively Exploited
Qlik Sense Exploited in Cactus Ransomware Campaign
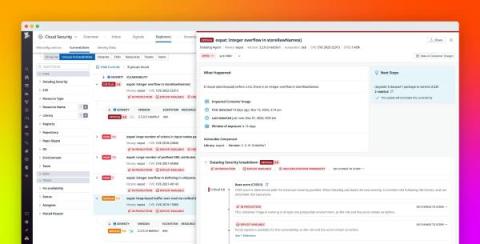
Mitigate infrastructure vulnerabilities with Datadog Cloud Security Management
Cloud environments comprise hundreds of thousands of individual components, from infrastructure-level containers and hosts to access-level user and cloud accounts. With this level of complexity, continuous and end-to-end visibility into your environment is vital for detecting, prioritizing, and fixing vulnerabilities before attackers can take advantage of them.
Exploring WebExtension security vulnerabilities in React Developer Tools and Vue.js devtools
Snyk's security researchers have conducted some research to better understand the risks of WebExtensions, both well-known (i.e. XSS, code injection) and those more specific to WebExtensions themselves. From our research we identified and disclosed some vulnerabilities within some popular browser extensions: React Developer Tools and Vue.js devtools. In this post, we will explore the WebExtension technology and look into the vulnerabilities identified.
CVE-2023-43177: Critical Unauthenticated RCE Vulnerability in CrushFTP
Trustwave MailMarshal Email Security Protects Against WinRAR Vulnerability CVE-2023-38831
The importance of email security cannot be understated. Proof of this can be seen in some recent research conducted by the Trustwave SpiderLabs team around our email security product MailMarshal. The team recently ran an experiment on known Zero Day CVE-2023-38831 found in RARLabs WinRAR that is currently being exploited in the wild in WinRAR versions 6.23 and earlier. WinRAR is a compression, archiving, and archive managing software tool.
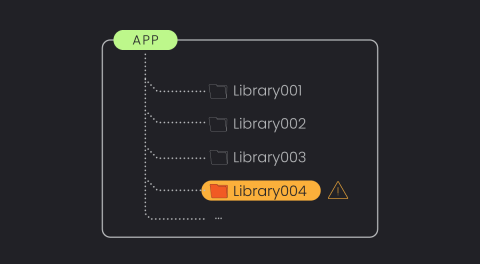
The Power of Library-Based Vulnerability Detection.
With an ever-growing number of vulnerabilities being discovered annually, vulnerability management tools are rapidly evolving to handle and prioritize these risks. However, it remains one of the most overwhelming and time-consuming areas in cybersecurity. There’s still significant room for enhancement, especially in reducing false alerts and prioritizing genuine threats.
Where to Get Hacker Attacks and Payloads #cybersecurity #applicationsecurity #cloudsecurity
File encryption in Python: An in-depth exploration of symmetric and asymmetric techniques
In our modern world, we constantly share private, confidential, and sensitive information over digital channels. A fundamental component of this communication is file encryption — transforming data into an unreadable format using encryption algorithms.