Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
How to scan your attack surface
In 2013, a group of ethical hackers started penetration testing to make the Internet a safer place. After hacking companies such as Google, Facebook among others, they realized they could automate their findings to help companies monitor their attack surface and founded Detectify. Fast forward a few years and Detectify’s Crowdsource network boasts of 400+ elite ethical hackers.
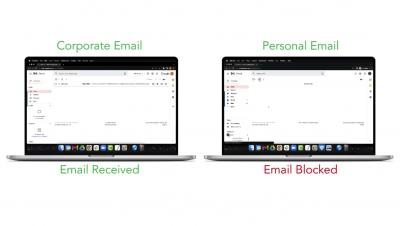
Adding the Save in 1Password button to your website just got way easier
Have you ever wanted to put a Save in 1Password button on your website? You can now add the integration to your website without anyone from 1Password building, approving, or getting involved with the process.
What's next for digital currencies?
Over the last two years, we’ve observed how digital assets have revolutionized payment and banking services. The explosion of interest in digital currencies brings with it new challenges in governance, privacy, competition, cybersecurity, and social inclusion. While a cashless future is still far away, more than 80% of central banks are either considering the launch of a central bank digital currency (CBDC) or have already done so.
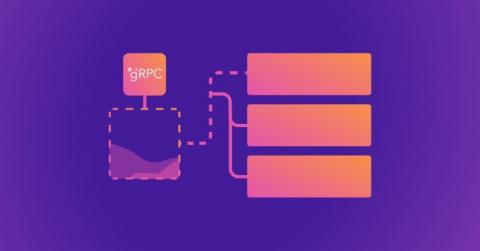
Building a secure API with gRPC
A Google remote procedure call (gRPC) is Google’s open source version of the remote procedure call (RPC) framework. It’s a communication protocol leveraging HTTP/2 and protocol buffer (protobuf) technologies. gRPC enables a remote client or server to communicate with another server by simply calling the receiving server’s function as if it were local. This makes communicating and transferring large data sets between client and server much easier in distributed systems.
The ReadOut: Falcon Long Term Repository
Rubrik and GraphQL - Episode 5 - Interfaces and Inline Fragments
What is the Dark Web?
The dark web is a part of the internet that provides anonymous and secure communication channels that are not able to be found by search engines. Numerous criminal activities are carried out on the dark web, such as the trafficking of stolen personal information, illegal sales of weapons and the trafficking of drugs.
Getting Started Guide: Falcon Long Term Repository
Limited data retention resulting from financial or technological constraints makes it hard for security teams to see the complete history of an attack. This lack of full context about a threat — or a potential threat — eventually catches up with organizations, leading to longer dwell times and increased risk of a breach.
Securing Cloud Infrastructure with Teleport and AWS Identity Federation
Over the last decade, enterprises have accelerated the adoption of the cloud. According to the State of the Cloud report by Flexera, the average annual spend on cloud computing is over $62 million. As enterprises continue to invest in the cloud, AWS, the market leader in cloud computing, is growing at a rapid pace. The rise of cloud computing poses new challenges to enterprise IT. With each department migrating and managing their workloads in AWS, there is a proliferation of accounts, users and roles.