Free hands-on security labs for your students
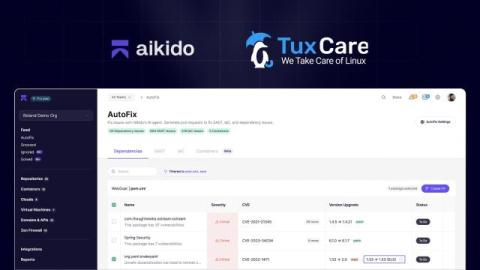
Whether you’re teaching computer science, software engineering, or cybersecurity, Aikido equips your students with enterprise-grade security tools, at no cost. Aikido for Education brings the same platform trusted by professional teams into the classroom, helping students learn by doing. Teachers can integrate it into their courses to give students hands-on experience with real-world security challenges, without adding complexity or cost. Curious about the “why” behind this program?