Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
CyberArk Secure Cloud Access Free Trial - Connect Your AWS Account in Minutes! | CyberArk
Want to secure your AWS environment with CyberArk Secure Cloud Access? This step-by-step tutorial will show you how to connect a standalone AWS account to the CyberArk platform during your free trial.
Lurking Threats in Post-Authentication Sessions
An attacker doesn’t need your password anymore. They don’t even need to break your MFA. They just need to get ahold of your session. And once they have it, they are you. Organizations have focused on securing access for two decades, initially relying on passwords. When passwords proved weak and insufficient, multi-factor authentication (MFA) emerged as the new standard. It was a substantial improvement, adding an extra layer of security to verify users.
How CISOs Can Use Identity to Advance Zero Trust
AI is the best thing that’s ever happened to cybercriminals. It allows them to weaponize trust and launch identity-based attacks with staggering scale and sophistication. I’m talking about mutating polymorphic malware, prolonged ransomware sneak attacks that lead to double-extortion and deepfakes that defraud victims every few minutes.
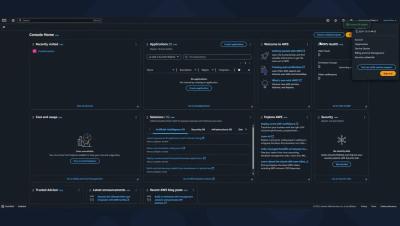
CyberArk Secure Cloud Access Free Trial: Platform Interface Guide | CyberArk
New to CyberArk Secure Cloud Access? In this walkthrough, we’ll guide you through the platform interface, helping you navigate key features during your free trial. What you'll learn: Overview of the Secure Cloud Access platform How to manage cloud access securely Essential tools & settings for AWS integration.
EP 3 - Building Trust in AI Agents
In this episode of the Security Matters podcast, host David Puner is joined by Lavi Lazarovitz, Vice President of Cyber Research at CyberArk Labs, to explore the transformative impact of AI agents on cybersecurity and automation. They discuss real-world scenarios where AI agents monitor security logs, flag anomalies, and automate responses, highlighting both the opportunities and risks associated with these advanced technologies.
EP 3 - Building Trust in AI Agents
In this episode of the Security Matters podcast, host David Puner is joined by Lavi Lazarovitz, Vice President of Cyber Research at CyberArk Labs, to explore the transformative impact of AI agents on cybersecurity and automation. They discuss real-world scenarios where AI agents monitor security logs, flag anomalies, and automate responses, highlighting both the opportunities and risks associated with these advanced technologies.
The Urgent Reality of Machine Identity Security in 2025
The importance of machine identity security has reached a critical juncture in 2025. With machine identities now far outnumbering human ones, securing these digital credentials has become a top cybersecurity priority for enterprises.
Unmanaged Endpoints: Your Security Blind Spot
It’s Monday morning and the coffee shop is full of telecommuters, sipping lattes and catching up on emails. The way organizations enable work has changed. With the rise of SaaS applications and cloud-first strategies, employees, contractors and third parties frequently access corporate assets from personal, unmanaged laptops.